Portland General Electric let us know we’ll be getting one of these before too long.
I was looking forward to it. I think I still am (because it sure seems like our monthly electric bills are high). But this article greatly dampens my forward look, so to speak:
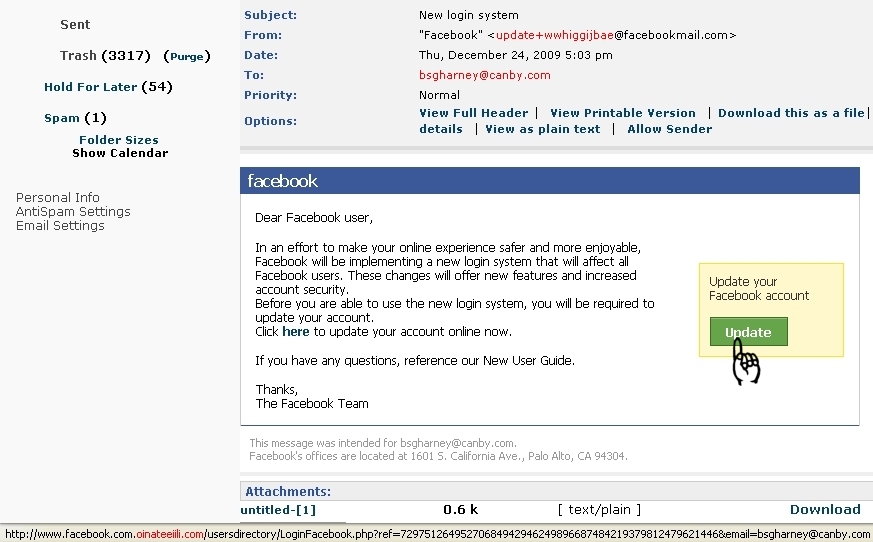
Computer-security researchers say new “smart” meters that are designed to help deliver electricity more efficiently also have flaws that could let hackers tamper with the power grid in previously impossible ways.
At the very least, the vulnerabilities open the door for attackers to jack up strangers’ power bills. These flaws also could get hackers a key step closer to exploiting one of the most dangerous capabilities of the new technology, which is the ability to remotely turn someone else’s power on and off.
The attacks could be pulled off by stealing meters — which can be situated outside of a home — and reprogramming them. Or an attacker could sit near a home or business and wirelessly hack the meter from a laptop, according to Joshua Wright, a senior security analyst with InGuardians Inc. The firm was hired by three utilities to study their smart meters’ resistance to attack.
[…]
Unlike traditional electric meters that merely record power use — and then must be read in person once a month by a meter reader — smart meters measure consumption in real time. By being networked to computers in electric utilities, the new meters can signal people or their appliances to take certain actions, such as reducing power usage when electricity prices spike.
But the very interactivity that makes smart meters so attractive also makes them vulnerable to hackers, because each meter essentially is a computer connected to a vast network.
[…]
But many security researchers say the technology is being deployed without enough security probing.
If hackers can get that far, what’s to keep them from hacking into my computers even when they’re off-line? (You know, entering my machines through the power plug instead of the phone jack.)
And what’s to keep governments from conspiring with manufacturers (or secret agents at manufacturing plants) to put “bugs” in electrical devices? The idea of my toaster or my bedside clock or my phone answering machine eavesdropping and tattling on me is not a pleasant thought. Maybe it’s time to come up with a not-so-new lifestyle mantra: Go Amish!
OK, so now I’ve given the kooks more material. Sorry. 🙄
Well, you can read the full article here: New ‘smart’ meters for electrical utilities have security holes